Hello all,
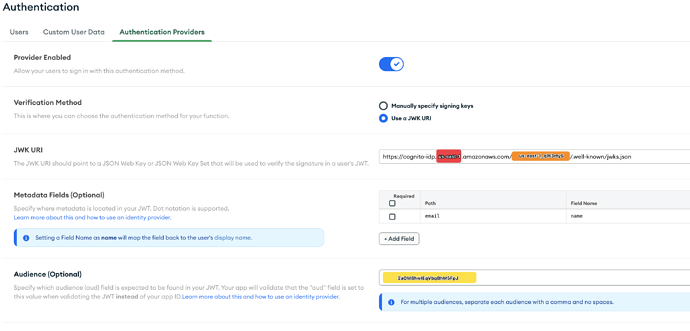
We are currently using AWS Cognito as our custom JWT authentication provider with our client Realm app. We have the whole flow working smoothly and have end-users interacting with our mobile app with no problems regarding authentication whatsoever. However, we have been trying to come up with a solution to creating backups of our infrastructure and data and getting stuck on one particular point, which is restoring user auth information.
When a user submits their credentials to Cognito, an Id token is retrieved from the response that has all the fields and information that we expect to see. This includes the ‘sub’ value. The ‘sub’ value is generated to be universally unique for each user by Cognito while a user is being created and is immutable. When the Id token is passed onto the Realm app as JWT credentials, a new app user is created if none exist or retrieved if it exists. Realm uses the ‘sub’ value received from Cognito and we can observe this in the identities array of the Realm app user object.
The catch, and the source of our problems, is that the ‘sub’ value generated by Cognito cannot be restored when restoring user data from backups. It is generated from scratch even if you are restoring a lost user account from an earlier backup and you know the previous ‘sub’ value. In such an event, since Realm keeps the old ‘sub’ value as the user’s identity, which is now lost, we have no means of linking this existing Realm user to their new ‘sub’ generated by Cognito.
We have been in contact with AWS about this and learned that we have no power over the ‘sub’ value or the token itself. So, we were hoping that there is a way for us to manage this from Realm. Ideally, we would be able to use a custom value as the value of the ‘id’ field within the identities array of the user instead of the ‘sub’ value automatically. However, we couldn’t figure out how to achieve this. So, we were wondering if there is a way of doing this without having to go the Custom Function Authentication route. Lastly, if that is a must, how would we go about migrating our existing Realm app users to this new method. Would that be done via identity linking?
Any help on this lengthy issue is very much appreciated.
-Cagri