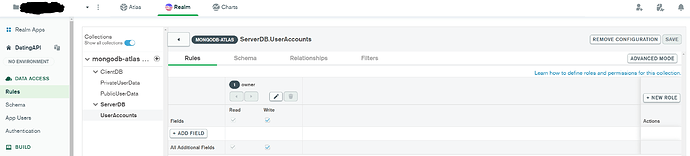
Hi there. I’m using the mongodb Realm and Atlas web UIs to manage my database serverlessly.
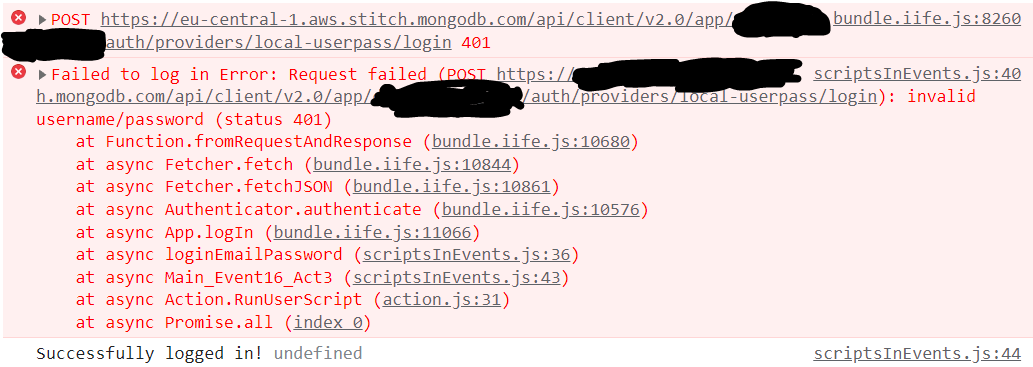
Now I’m having a big problem. I accidentally found out (because there are no warnings or hints except well hidden in the documentary…!) that even when I have enabled and set up authentication and thoroughly configured role restrictions that still anyone on the whole planet can access and read all of my database data.
WHY on earth would a company even default that?! This is so careless and dangerous, I almost can not believe that. I have sensible data (steam codes) in the database and thought having user authentication and role restrictions is enough to protect them. Nooooo because the mongo developers seem to not value security at all. By default everyone on the internet is invited to steal my data.
And there is no option that I can change that in the mongodb Realm web dashboard.
So for a basic security feature, where it should be very plausible to lock and close all virtual doors by default, I need to download stuff and learn how to use some 1980’s command shell stuff. Great.
Please imagine this: I was able to create, manage, update, delete, read a database and what not without touching a single command shell. But for making it secure I need to do that? Sorry that doesn’t look like a very reputable practice to bait novice people into using your, as so easy to use and fast to setup, product and then not protect these users by default.
I hope the development team will show mercy and implement these 4 lines of code asap, so that normal people who are not programmers can also have security. That’s one of the purposes of Realm I guessed.